You might have heard about WebRTC leak and ways to prevent it. WebRTC is often talked about on VPN websites. What exactly is WebRTC and what’s the havoc it causes?
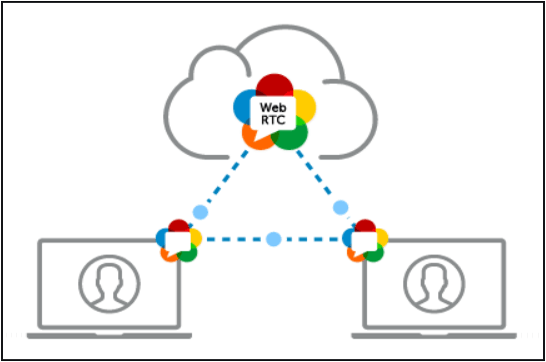
WebRTC is a technology that allows your browser to have video and voice communication abilities. It might seem like an annoyance when you think about the leaks it causes, but it’s actually a great technology.
When you use Google Meet to hold a video conference, you’re using WebRTC. The same is with the Facebook Messenger video call. There are other applications that make use of WebRTC. For example, if you’re on Discord, you use WebRTC.
Basically, if you’re voice or video calling on your browser, you’re using WebRTC. Without this feature, your browser will be severely limited in its abilities. And with this feature, you don’t need any extra plugins for voice and video communication.
All major browsers (Mozilla Firefox, Google Chrome, MS Edge, Apple Safari, Opera, etc.) come with WebRTC capabilities. In fact, it is used in many mobile apps as well. It is a completely free technology and is open source. Since it is open source, it is improving and evolving to offer better services.
It enables live communications in real time.
Now, what is WebRTC leak?
WebRTC works by sending audio/video feeds between two entities. For this, it established communication channels from the browser to the website you open. This means your browser will share some of your information with the website, which will include your IP address. And these channels can bypass the encrypted tunnel you have setup. So basically, a WebRTC leak can reveal your real IP address even if you are using a VPN.
Imagine this scenario: You’re using a VPN and want to have a voice call with someone so you need to use WebRTC. But it will leak some data so your real IP will get shown on the website side. This beats the entire purpose of using a VPN. A channel that bypassed the tunnel you’ve created – it’s scary.
How to know about a WebRTC leak?
To see if your IP is leaked, just connect to a server and run a leak test. If you see your real IP on the website, your IP is being leaked. But if you can see the IP address of the VPN server, you’re safe and your browsing is secure.
What to do if your WebRTC is leaking your details?
The good thing is that WebRTC leaks can be blocked.
Here’s how you can block the WebRTC leak
There are many ways to block the WebRTC leak. One way is by getting a VPN that doesn’t allow these leaks. These VPNs will let WebRTC work but only through the encrypted tunnel.
Another option is to block the WebRTC requests directly from the browser. You can also use browser extensions if you cannot disable WebRTC.
Keep in mind that if you disable WebRTC, you won’t be able to enjoy the functionalities that come with it.
Disabling WebRTC in Chrome
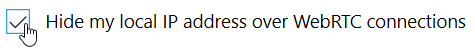
You cannot disable WebRTC in Chrome. The only thing you can do is use add-ons. A good Chrome add-on is WebRTC Leak Prevent which is fast and powerful. It controls the hidden WebRTC settings and protects you against the leaks. Of course, when you use this, you won’t be able to use a WebRTC based service.
Disabling WebRTC in Chrome mobile
1. Type this URL chrome://flags/#disable-webrtc in your Android Chrome address bar. It will open a settings page.
2. Scroll down and you’ll find WebRTC STUN origin header. You can disable it here.
3. You can even disable WebRTC hardware video encoding and decoding options if you want.
Disabling WebRTC in Mozilla Firefox
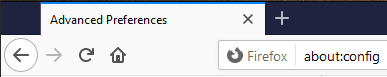
1. Go to the URL bar, type about:config and press enter

2. Firefox will display a warning message. Click on I accept.

3. It will take you to another page. In the Search bar, type media.peerconnection.enabled

4. Double click on the row and change its value to false

Now WebRTC will be disabled on the browser.
Disabling WebRTC in Opera
Opera doesn’t have a way to disable WebRTC so you can use third-party addons like WebRTC Leak Prevent just like you did with Chrome. Keep in mind that these extensions do not fix the leak. Instead, they block the attempts the websites make to collect IP addresses.
So even if you use these extensions, the website might be able to get your data through cookies. However, if you use a safe browser like Kingpin that deletes cookies after each session closes, your data will be safe and you won’t be tracked by website trackers.
Disabling WebRTC on Safari browser
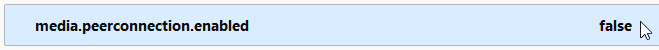
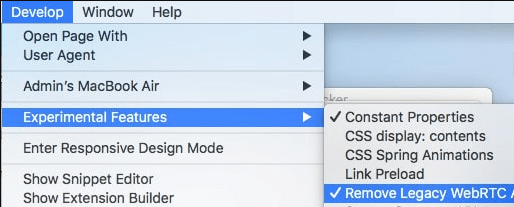
1. On Safari, visit Preferences

3. In the Develop section, go to Experimental Features
 Remove Legacy WebRTC API”>
Remove Legacy WebRTC API”>
4. Click on Remove Legacy WebRTC API
Disabling WebRTC on Microsoft Edge
You’ll find WebRTC and ORTC (Microsoft’s proprietary version of WebRTC) on Edge. While you cannot disable it on Edge, you can certainly hide your real IP address. Here’s how you can do it.
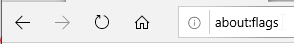
1. Visit MS Edge and type about:flags in the address bar. Press enter.

2. You’ll see WebRTC here. Under that, there’s an option to hide your real IP address. Check the box to activate it.

Will it work if you install VPN on the router instead of the browser?
You might think WebRTC leaks happen because you’re using a VPN plugin on your browser. But that’s not true. Even if you use a VPN on your router, it will do nothing to fix the leak issue. You’ll need to follow the methods discussed above.
How to stay secure
To stay secure online, make sure you use a VPN. And the VPN should be able to bypass the WebRTC leak. With a VPN, you can use a secure browser like Kingpin that does not keep any of your details. There is absolutely no history on records and it’s like you’re on incognito all the time.
Of course, you can disable WebRTC on several browsers but there are many steps involved. Also, after disabling WebRTC, you might not be able to enjoy the internet as you do now. A better option is to use a trusted VPN.
When selecting a VPN, read their reviews about WebRTC and discuss it with their customer service. If they confirm that they’re able to block WebRTC leaks, only then get that VPN. And to be secure, you can get a VPN that offers a money back guarantee so that if their claims don’t work, you can claim a refund.




 Remove Legacy WebRTC API”>
Remove Legacy WebRTC API”>